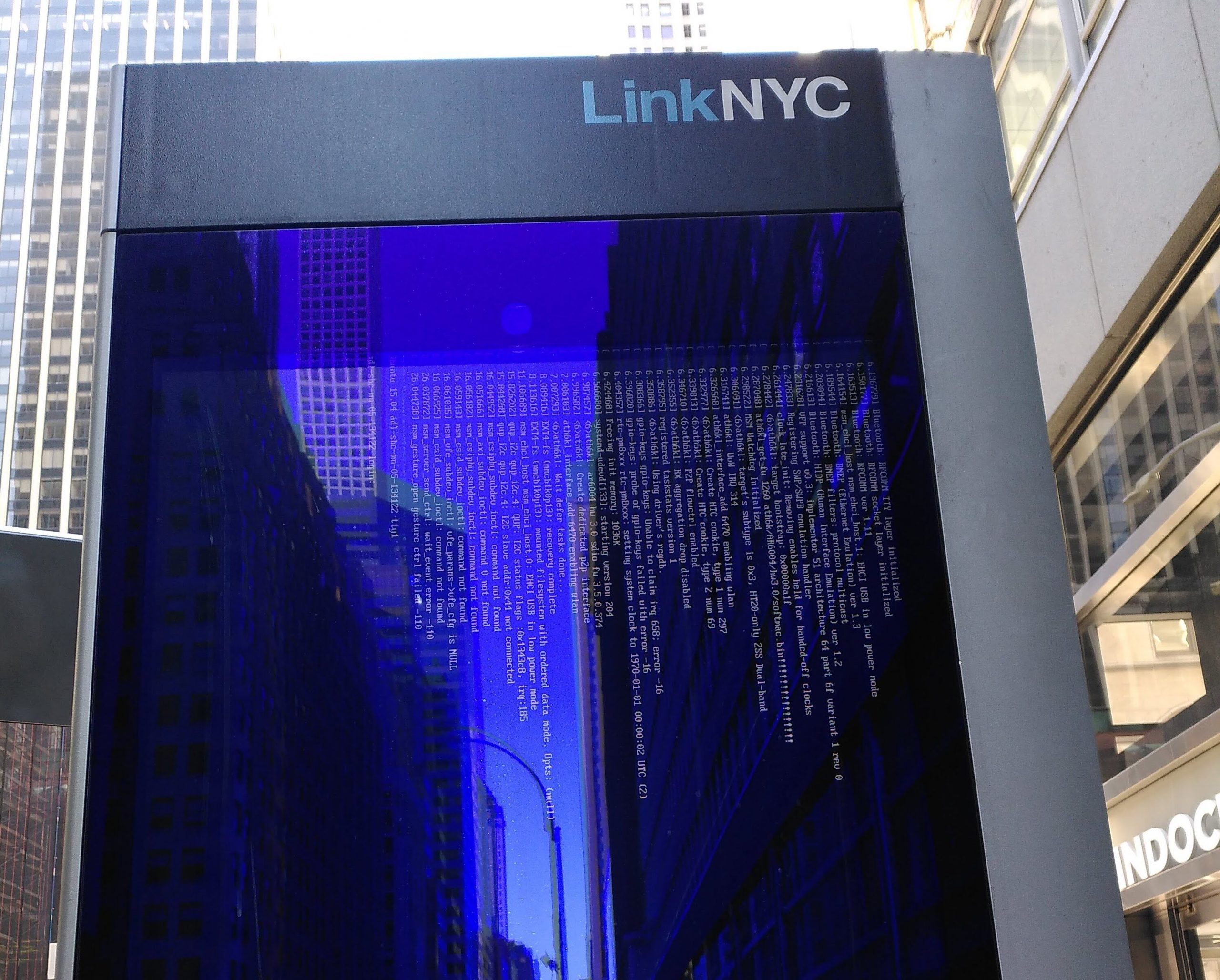
We remember stories. And the Crowdstrike-caused massive Windows outage is a good story.
If you work in Delta Airlines IT, you won’t forget this story anytime soon. As millions of passengers are stranded and separated from their luggage, you will probably see your CEO hauled in front of Congress for public shaming.
If you are responsible for some of the around 10 million Windows computers that Crowdstrike, in their incompetence, managed to bring down, you are also likely to remember.
But if you dodged the bullet this time, the whole debacle will become just another tech story in your news feed and quickly forgotten.
However, there are lessons to be learned about canary deployment, robustness against poisoned data, and undocumented software dependencies. To ensure your organization makes the most of this opportunity, have someone read the Crowdstrike Preliminary Post Incident Review and tell the story at your next department meeting. Have them tell everyone why it happened and why it couldn’t happen to you. Or why it could have happened to you, but for the grace of God.
A continually learning organization needs a way to make knowledge stick in its people’s brains. Storytelling is an excellent way to do that. Always be on the lookout for good stories.